Legacy modernization rarely fails because engineers can’t refactor. It fails because organizations can’t stomach the risk. Security teams worry that “AI refactoring” means proprietary code leaving the building. Platform teams worry an agent will run the wrong command, touch the wrong directory, or quietly introduce behavior changes that only show up in production. And engineering leaders worry that a massive monolith rewrite will become a multi-quarter outage factory.
This is where Anthropic Claude Code and the newer Claude Code Security capabilities change the conversation. Instead of treating AI as a black-box rewrite engine, Claude Code is designed around permissioned actions, constrained file system boundaries, and human-reviewed changes. Paired with Claude 3.7 Sonnet’s hybrid reasoning (including extended thinking), teams can modernize technical debt with a local-first workflow that reduces both security exposure and refactoring breakage risk.
Why legacy enterprises fear AI refactoring
Most enterprise hesitation clusters around two failure modes:
- Security and data leakage: Source code, configuration, and secrets are high-value assets. Even “harmless” context like internal API routes, RBAC rules, or error messages can be sensitive. Enterprises want clear boundaries on what can be sent to a model and what must stay local.
- Refactoring breakage: Monoliths accumulate hidden coupling: global state, side-effectful helpers, implicit contracts, and “temporary” flags that became permanent. A sweeping refactor can regress behavior, create performance cliffs, or break builds in ways that are expensive to debug.
Traditional modernization tools help, but they tend to be either too narrow (rule-based codemods that can’t reason about domain logic) or too risky (agents that can freely execute commands, fetch network content, and modify arbitrary paths). Claude Code’s design tries to de-risk those exact edges.
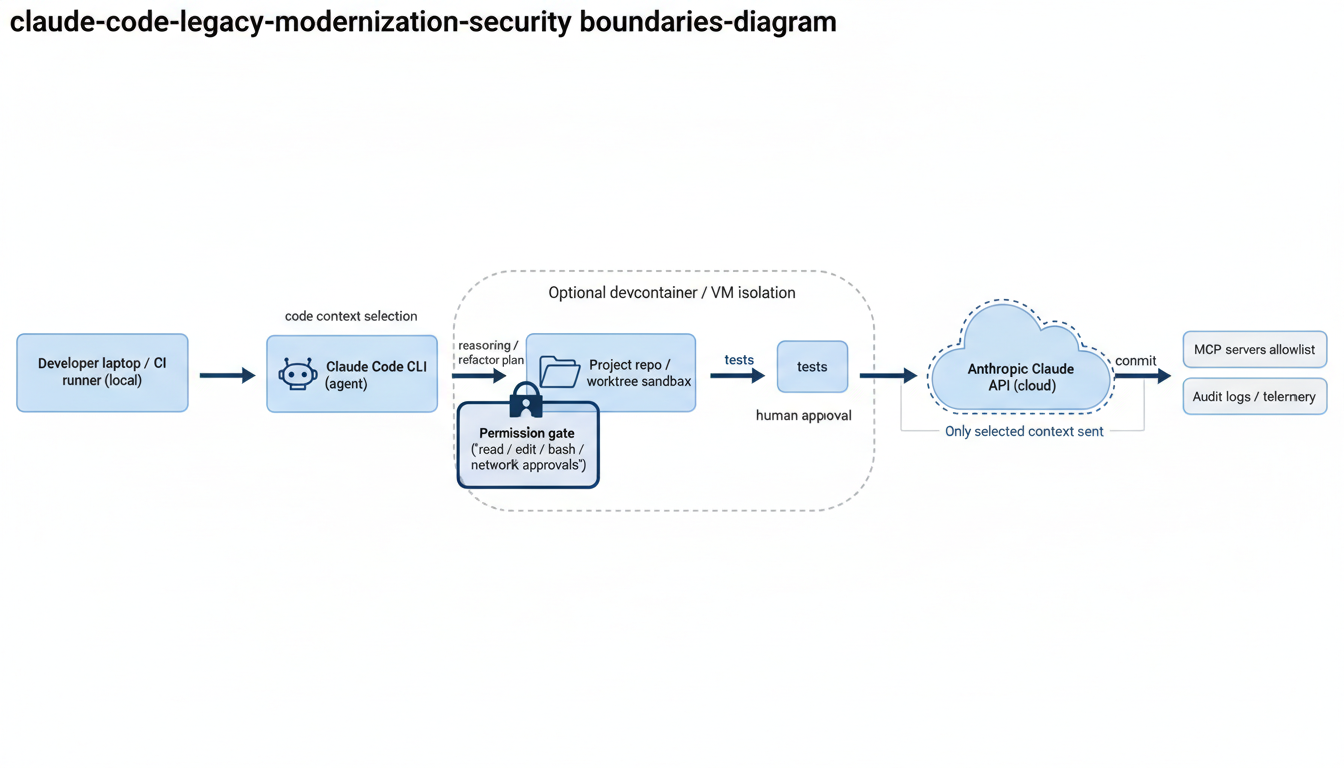
What Claude Code changes: permissioned, local-first agentic refactoring
Claude Code is an agentic CLI that can read code, edit files, and run commands, but it is built around a permission model and explicit boundaries. According to the Claude Code security documentation, it uses strict read-only permissions by default, and requests explicit approval for actions like editing files or running commands. It also restricts write access to the directory where it was started (and subfolders), creating a clear “project scope” boundary. It can additionally block risky commands (for example, web-fetching utilities) by default and require approvals for network requests. These controls are designed to reduce both accidental damage and prompt-injection style risk when working with untrusted inputs. (Claude Code security docs, updated in the live documentation.)
In practice, this turns “AI refactoring” into something closer to a supervised automation tool:
- You choose the working directory (the repo or a dedicated worktree) and keep the blast radius tight.
- You approve side effects (edits, bash commands, network access) rather than hoping the agent behaves.
- You can enforce organizational settings (for example, consistent permissions and MCP allowlists) so teams modernize the same way across many repos.
CLI controls that matter for enterprise risk
The Claude Code CLI reference documents a set of flags that are especially relevant when you’re modernizing legacy systems under compliance constraints:
- Worktree isolation:
claude -w <name>starts Claude in an isolated git worktree, which is ideal for parallel refactors and for ensuring the agent’s changes are compartmentalized. (CLI reference) - Permission modes and tool restriction:
--permission-modeplus--tools,--allowedTools, and--disallowedToolslet you explicitly scope what the agent can do in that session. (CLI reference) - Budget and turn limits:
--max-budget-usdand--max-turnshelp prevent long-running sessions from ballooning cost or scope during large refactors. (CLI reference) - MCP strictness:
--strict-mcp-configand--mcp-configsupport a controlled server list for tool integrations, aligning with the docs’ guidance that MCP servers should be allowlisted and trusted. (CLI reference + security docs)
These options let you treat Claude Code like any other enterprise developer tool: configured, constrained, auditable, and standardized.
How Claude Code Security reduces the “we’ll ship a vulnerability” fear
Claude Code Security (announced by Anthropic as a limited research preview) is positioned differently than typical SAST tooling. Instead of rule matching, it reads and reasons about code “like a human security researcher,” tracing data flow and component interactions. Anthropic describes a multi-stage verification process to reduce false positives, plus severity and confidence ratings, and emphasizes that fixes are human-reviewed rather than auto-applied. (Anthropic announcement: “Making frontier cybersecurity capabilities available to defenders.”)
For legacy modernization, this matters because the riskiest refactors are rarely syntactic. They tend to touch:
- Authorization checks embedded in “service” code
- Input validation split across layers
- Session handling, token parsing, and implicit trust boundaries
- Business logic that accidentally enforces security policy
A reasoning-based review step is valuable precisely where monoliths hide security logic in unexpected places. Used correctly, it becomes a gate that helps modernization move faster, not slower: you do the refactor, then you run a security-focused pass over the changed surfaces before merging.
Using Claude 3.7 Sonnet’s reasoning to refactor monoliths safely
Claude 3.7 Sonnet was announced on February 24, 2025 as Anthropic’s first “hybrid reasoning” model, supporting both near-instant responses and extended thinking with an API-controlled “thinking budget.” Anthropic also introduced Claude Code alongside it as a limited research preview. (Anthropic announcement: “Claude 3.7 Sonnet and Claude Code.”)
Why this matters for legacy refactoring: the hardest part of modernizing a monolith is building a correct mental model of coupling and invariants. Claude 3.7 Sonnet’s strength is in planning multi-step changes, not just generating code. In modernization work, you want the model to produce:
- A refactor plan broken into safe increments (each with rollback)
- Assumption checks (“where is auth enforced?”, “what headers are required?”, “what’s the canonical time zone?”)
- Test expansion proposals targeting regression-prone logic
- API boundary mapping for incremental extraction
On pricing, Anthropic’s API documentation lists Claude 3.7 Sonnet pricing at $3/MTok input and $15/MTok output (and notes it is deprecated in the current pricing table), while newer Sonnet models maintain the same baseline token prices. (Claude API pricing docs.)
A practical modernization workflow (with guardrails)
Below is a pattern that works well when you need to modernize legacy systems without losing control of security and correctness. It leans on Claude Code’s permission model, git worktrees, and a security review step.
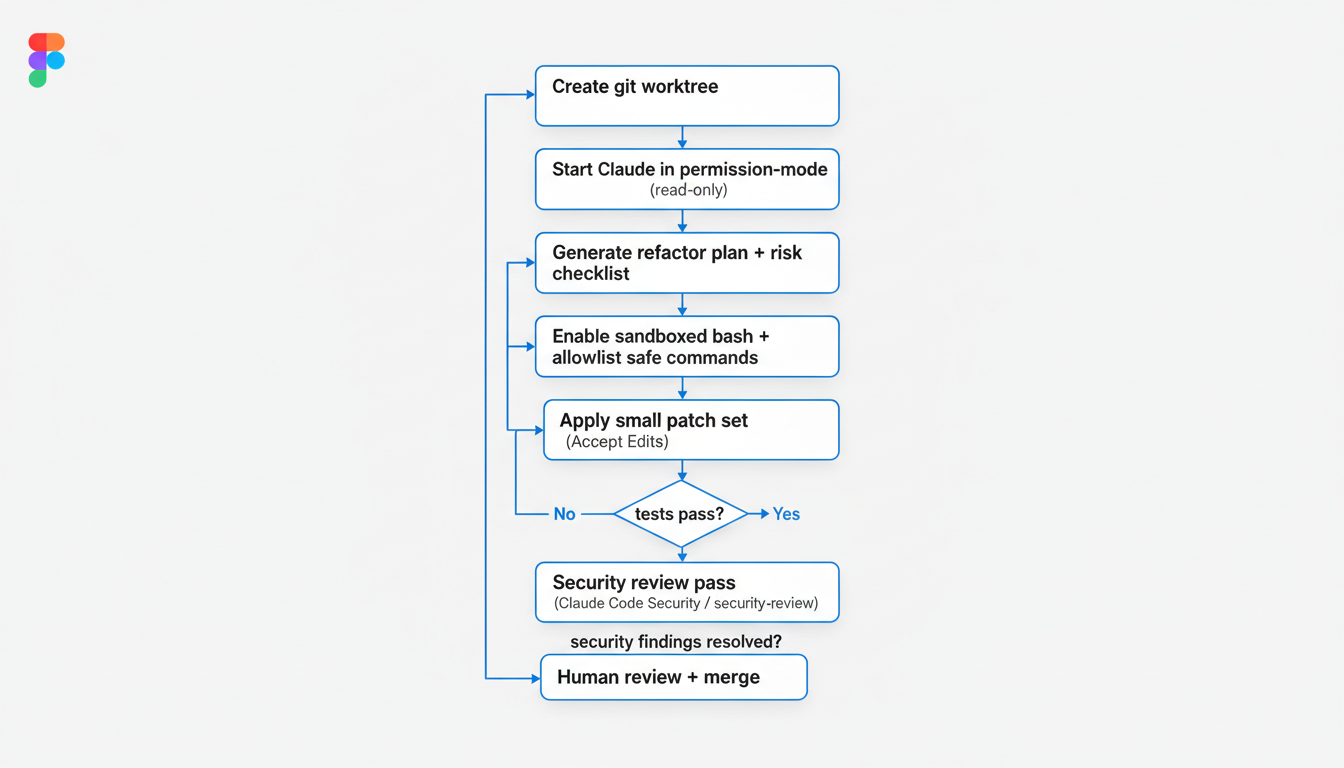
- Start in an isolated worktree
Use a dedicated branch or a Claude Code worktree so changes stay contained. - Begin in planning mode (read-only)
Ask Claude to map modules, dependencies, and risk hotspots before any edits. - Define “do not touch” and “must prove” constraints
Examples: no auth changes without approval; must keep API behavior identical; must add tests for each behavior change. - Allow only the tools you actually need
Prefer restricting tools to Read/Edit plus a small bash allowlist (tests, lint, type-check) to avoid accidental side effects. - Refactor in small patches
Extract functions, add types, split modules, remove dead code, and update dependency seams incrementally. - Gate every patch with tests
Run unit tests, integration tests, and static checks after each step to keep regression scope small. - Run a security-focused review pass
Use Claude Code Security where available, and always do human review for anything touching auth, crypto, or validation. - Merge with standard engineering discipline
Code review, CI, deployment rings, and rollback plans are still non-negotiable for legacy systems.
Concrete examples: refactoring without exposing proprietary data
“Local-first” in this context doesn’t mean “no cloud model.” It means you control what context is shared, and you keep the operational environment (repo, tools, secrets) inside enterprise boundaries. Claude Code’s security model helps enforce that by defaulting to read-only and requiring explicit approvals for edits, commands, and network access. (Claude Code security docs.)
Three practical patterns that reduce exposure:
- Minimize context by design: Ask Claude to operate on a module at a time and to request files explicitly, rather than dumping the whole repo into a prompt.
- Redact or stub sensitive config: Keep production secrets and customer identifiers out of the working tree. Prefer sample configs and environment-variable references.
- Block network tools by default: Avoid letting the agent fetch remote content during refactors. The Claude Code docs explicitly call out network request approval and default blocks for risky web-fetching commands. (Security docs.)
When you need stronger isolation, the security docs also recommend approaches like using devcontainers for additional containment. That’s a good fit for legacy modernization because you can freeze dependencies, reproduce builds, and keep the agent in a predictable sandbox.
Example: scripting a “plan-first” refactor session
This is an illustrative pattern using documented CLI flags to keep sessions constrained. Adjust tool lists to your stack and compliance requirements.
# Start in an isolated worktree
claude -w payments-refactor
# Plan first. Limit tools and turns; cap spend; keep output machine-readable when needed.
claude -p \
--permission-mode plan \
--tools "Read,Grep,Glob" \
--max-turns 3 \
--max-budget-usd 2.50 \
"Map the payments module boundaries, list implicit contracts, and propose a 5-step refactor plan with tests for each step."Once the plan looks right, you can open a new session that allows a narrow set of safe commands (for example, running tests) and apply the refactor incrementally.
Feature comparison: legacy modernization risk controls at a glance
The point of Claude Code in enterprise modernization isn’t that it can edit code. Many tools can. It’s that it combines agentic refactoring with explicit guardrails and a security-focused workflow.
| Concern | “Old way” modernization pattern | Claude Code + Claude Code Security approach |
|---|---|---|
| Accidental destructive changes | Scripts/codemods run broadly; hard to reason about blast radius | Write access restricted to the started directory; explicit permission prompts for edits/commands; worktree isolation for containment |
| Prompt injection / untrusted inputs | Agents ingest arbitrary text; unclear tool boundaries | Permission system, command blocklists, network request approvals, trust verification for new codebases/MCP servers (per docs) |
| Security regressions in refactors | Rule-based scans catch patterns, miss business logic flaws | Claude Code Security reasons about data flow, component interaction; multi-stage verification; severity/confidence; human-reviewed patches |
| Runaway scope and cost | Refactors sprawl; “one more change” syndrome | CLI controls like max turns and max budget; structured, incremental plans; test gates per step |
| Enterprise standardization | Each team invents process; hard to audit | Managed settings, allowlists, and repeatable CLI configurations; monitoring and audit-friendly workflows |
Implementation checklist for enterprise adoption
If you want to use Anthropic Claude Code for legacy refactoring without triggering security and reliability objections, treat it like a platform capability, not a developer toy.
- Define a default permission posture: start read-only, require approvals for bash and network, and keep a short allowlist of safe test commands.
- Standardize worktree-based refactors: every modernization task runs in an isolated branch/worktree with CI gates.
- Adopt “plan-first” sessions: require a written change plan plus a risk checklist before any edits for high-impact modules.
- Integrate security review into the loop: run Claude Code Security (where available) and keep human sign-off for auth/crypto/input validation.
- Log and audit: capture tool approvals, commands executed, and diffs as part of the modernization evidence trail.
- Train engineers on prompt hygiene: avoid piping untrusted content directly to the agent; verify commands before approval (explicitly recommended in the security docs).
Conclusion
De-risking legacy modernization is mostly about control: control over what leaves the repo, control over what the agent can execute, and control over how changes are validated. Claude Code’s permission-based architecture, bounded write scope, and configurable tooling reduce the “AI can do anything” fear that stalls adoption. Claude 3.7 Sonnet’s reasoning helps where legacy systems are hardest: planning safe increments, identifying implicit contracts, and proposing tests that keep refactors honest. And Claude Code Security adds a security-first review layer aimed at catching subtle, context-dependent vulnerabilities that pattern matching tools often miss.
Next steps: pilot Claude Code on a single bounded modernization target (one module or service seam), enforce worktree isolation and strict permissions, and measure outcomes using concrete metrics: lead time per refactor step, test coverage growth, regression rate, and security findings before merge. Modernization doesn’t have to be a leap of faith. With the right guardrails, it can be an iterative, auditable engineering practice.